Simple Password Rules Every Senior Should Know to Stay Safe Online
You use logins every day for banking, health records, and email. Scammers often aim at older adults because they hope you are busy, trusting, or new to some online tricks. Knowledge gives you control.
In this short guide, you will learn easy steps that take minutes: use longer passphrases, stop reusing the same login details, and add a second step like verification codes on important accounts. These habits cut the odds that a scammer can access your money or identity.
Imagine an urgent email saying “your bank account is locked” that pushes you to sign in on a look‑alike site. That is how thieves try to rush you. The steps here show how to spot that and avoid it.
I’m Dan Alex. I’ve taught adults how to use technology safely for over 15 years. You don’t need to be a tech expert—just consistent with a few simple rules. This guide also explains how criminals steal logins, how to stop them, and what to do fast if something goes wrong.
Why seniors are targeted online and why passwords matter today
Attackers look for accounts that unlock banks, medical portals, and government services. You hold information that can be turned into money, identity theft, or access to sensitive health records and Social Security details.
Here are common real-world scams: an email asks you to “act now” and demands your login, a message claims your Medicare or Social Security is paused, or a fake bank notice urges you to reset a password. These are designed to rush you into giving information.
- Stolen logins can lead to unauthorized transfers, shopping charges, or medical portal access that exposes health data.
- A scammer who controls your email can click “Forgot password” and take over other accounts without guessing new credentials.
- Social Security-related information helps crooks open accounts, pass identity checks, or answer security questions.
Data breaches happen when companies are hacked and logins leak. HaveIBeenPwned lists nearly 15 billion exposed accounts, so reused credentials multiply your risk. You can block most takeovers by securing your email first and using unique login details.
| Threat | Example | Quick red flag |
|---|---|---|
| Email takeover | Criminal uses forgot-password links to access bank and health accounts | Unexpected password-reset emails |
| Phishing message | Fake Social Security alert asking you to sign in | Urgent language or threats |
| Breached login reuse | One leaked password opens several accounts | Same credential used on many sites |
Next, you will learn how a single login works and the common ways criminals try to crack it.
What a password really does and how criminals try to break it
Think of your password as the key to your online front door. A password is what you know. If someone copies that key, they can try it on any site where you used the same login.
Three simple ways to prove it’s you
There are three common ways websites check your identity:
- What you know — a password or PIN.
- What you have — a phone, an ATM card, or a security key.
- Who you are — a fingerprint or Face ID.
Single-factor versus multi-factor in plain language
Single-factor means one lock: just a password. Multi-factor means adding a second lock. An ATM is a clear example — card plus PIN. That extra step makes it much harder for a thief.
| Method | Example | Why it helps |
|---|---|---|
| What you know | Password or PIN | Easy to remember, but can be copied |
| What you have | Phone or card | Needs physical device |
| Who you are | Fingerprint or Face ID | Unique to you |
Criminals try three main ways to break in: guessing weak strings, using leaked credentials from breaches, and tricking you into entering a login on a fake page. Many sites and apps now send verification codes to block takeovers.
Next you will build a strong passphrase that is hard to crack but simple for you to remember today.
Safe passwords for seniors tips you can follow in five minutes
A short routine lets you create a strong passphrase without memorizing random characters. In about five minutes you can follow a simple recipe that makes a long, memorable login you will actually use.
Pick a phrase and make it longer
Choose a harmless sentence you like. Remove the spaces and keep at least 12–15 characters; 20 is even better. Length matters more than clever substitutions.
Mix letters, numbers, and symbols the easy way
- Write four or more words: a sentence works best.
- Remove spaces and capitalize a few letters you’ll remember.
- Add two numbers and one symbol in a fixed spot (for example, end with !7).
What to avoid and a simple method
Don’t use common patterns like 123456, Password, qwerty, or long keyboard runs such as qwertyuiop. Skip birthdays, addresses, grandkids’ names, or team names—scammers often find those online.
Sentence-method example and samples
Example: “The Old Duke is my favorite pub in South London” → ThOlDuismyfapuinSoLo.
Other real-world samples: myb!rDP0lly#1!, D0m8inma$ter@. They work because they are long, mixed, and not personal.
Quick self-check before saving: is it long enough, not personal information, not a common string, and not reused anywhere else?
Make every account safer by never reusing passwords
When one website exposes your credentials, other accounts are at risk too. A single leaked login can let someone try that same combination on banking, email, or pharmacy sites and gain access quickly.
How one leaked password can lead to multiple account takeovers
If a small shopping site is breached, criminals often test the stolen email and password on larger services. If they get into your email, they can request password resets everywhere else.
Where reuse hurts most: email, banking, shopping, and health portals
- Email — attackers use it to reset other accounts.
- Banking / bank — money can be moved or cards charged.
- Shopping — saved cards and orders can be abused.
- Health — private records and prescriptions can be exposed.
An easy system for unique passwords without sticky notes on your computer
Keep one long personal passphrase you can remember, then add a short site tag you invent. Example: “GreenRiverWalk!7” + “-AMZ” becomes GreenRiverWalk!7-AMZ for Amazon, and GreenRiverWalk!7-PHR for a pharmacy portal.
Do not store logins on your desktop or tape them under the keyboard. If you must write something down, keep one paper list in a locked drawer until you set up a password manager.
| Risk | Example | Quick action |
|---|---|---|
| Email takeover | Criminal uses reset link to change bank login | Change email passphrase, enable 2FA |
| Shopping breach | Saved card details stolen from site | Change site passphrase, check cards |
| Health portal exposure | Medical records viewed or altered | Update passphrase, notify provider |
Mini-checklist: secure your email first, then bank, then health, then shopping subscriptions. After that, add a second lock (2FA) to protect even strong passphrase-based accounts.
Add a second lock with verification codes and authentication apps
Add an extra step that asks for a one-time code after you enter your login. This is called two-factor or multi-factor authentication (2FA/MFA).
How a text code works
After you type your username and secret, the site sends a code to your phone. You enter that code to finish signing in. That second check stops many account takeovers.
Why an authenticator app can be better
Apps generate codes on your device instead of sending them by text. That reduces the risk of criminals intercepting SMS messages.
Priority checklist and quick actions
- Email — protect this first, since it controls resets.
- Banking — add MFA to bank and credit accounts next.
- Health portals — enable codes on medical and pharmacy accounts.
- Shopping and social — turn on MFA where available.
Step-by-step phone guidance
Open Settings, look for “Passwords,” “Security,” or “Two-Factor Authentication.” In apps, find Security or Account settings and follow the enable prompts. Make sure you save backup codes and confirm recovery phone or email.
| Action | Example | Why it helps |
|---|---|---|
| Enable 2FA | Gmail, Apple ID, Microsoft | Protects password resets across accounts |
| Use an app | Authenticator apps | Less vulnerable than SMS |
| Store backups | Printed codes in a drawer | Helps restore access if phone is lost |
Use a password manager the safe way (free and built-in options included)
Let a manager do the heavy lifting: it stores and creates unique credentials for each site so you stop reusing the same login. A good password manager remembers every entry and can generate long, random strings you would not guess.
Why it helps and where to start
It ends reuse immediately and removes the need to memorize dozens of passwords. Many phones and browsers include built-in manager features you can enable at no extra cost.
Quick setup steps
- Install or enable a manager on your phone and browser.
- Import saved logins if offered, then replace weak or repeated passwords over time.
- Create a strong master passphrase using the same long, nonpersonal method described earlier.
Extra protection and recovery
Turn on multi-factor authentication for the manager so someone needs more than the master to gain access. Set a recovery email or phone, save backup codes, and keep an emergency copy in a locked drawer or home safe.
On writing down one master
It is acceptable to write down one master if you store it securely at home. Also, make sure the email tied to your manager has MFA so attackers cannot hijack recovery and access your vault.
Simple habits that protect your accounts over time
Small daily habits make a big difference in keeping your online accounts under your control.
When to change a password and when you don’t need to
Change a password right away if you get a breach notice, suspect a scam, or know you reused that login. In those cases, update the account and enable multi-factor authentication.
Don’t change passwords constantly without cause. Constant resets create more confusion and can lead to unsafe shortcuts over time.
How to spot a fake login page before you type
Before typing, check the website address in the browser bar for misspellings or extra characters. Look for HTTPS and a padlock, but know those alone do not prove legitimacy.
If a message urges you to act instantly, pause and type the site address yourself instead of following links. Scammers often send “package delivery problem” texts that lead to fake login pages.
Safer sign-in habits for banking and sensitive accounts
Always open your bank by typing the bank’s address or using the official app. Your bank will not ask for your password in an email.
A quick routine: type the site, confirm the address, then sign in. This reduces the chance a scam link gives someone access to your money.
Public devices and HaveIBeenPwned
On shared computers log out and close the browser when you finish. Leaving a session open lets the next person gain access.
Use HaveIBeenPwned to check exposure: enter your email, review any breaches, then change affected passwords and enable MFA where possible.
| Action | When | Why |
|---|---|---|
| Change password | After breach notice or suspected reuse | Stops attackers who use leaked credentials |
| Type website yourself | Before banking or email sign-in | Avoids fake pages from links |
| Log out on public devices | Every time | Prevents others gaining access |
Quick habit checklist to print
- Secure your email first, then bank and other accounts.
- Use unique passwords and enable MFA everywhere available.
- Take your time — don’t let urgency push you into a mistake.
- Avoid clicking email links for sign-in; type the site instead.
What to do if something goes wrong (and how to recover quickly)
A calm, step-by-step response is the fastest way to regain control after an incident. Mistakes happen, and acting quickly protects you now. Below are clear actions to reduce harm and restore access.
If you think your password was stolen
Change that login immediately. Use a long, unique phrase and sign out of other sessions if the website offers it.
Turn on multi-factor authentication so someone needs more than the secret to gain access.
If your email was taken over
Start the provider’s recovery process right away and reset the email password.
Check forwarding rules, recovery addresses, and recent activity. Then reset important accounts linked to that email, such as banking and medical portals.
If you clicked a suspicious link
Disconnect from Wi‑Fi or cellular data immediately. Run a full scan with a reputable antivirus app before signing in anywhere else.
Do not enter credentials until the device is clean. Take screenshots or save the message for reporting.
Protecting your identity and financial accounts
Contact your bank and credit card companies at once. Ask them to watch for unusual charges and to add extra security notes on accounts.
Review your credit reports at AnnualCreditReport.com and consider a credit freeze to stop new accounts opening in your name.
If Social Security information may be exposed, document what happened and contact the agency or your benefits office for next steps.
Where to report scams and phishing in the US
Forward phishing emails to spam@uce.gov and reportphishing@apwg.org.
Also report fraud to your bank, the company involved (website or app), and to the FTC if needed. Write down date, time, message text, and the website address—you may need this when banks or investigators ask questions.
| Situation | Immediate action | Follow-up |
|---|---|---|
| Stolen password | Change login, sign out other sessions, enable MFA | Check linked accounts and monitor activity |
| Email takeover | Use recovery, change email passphrase, remove forwarding | Reset passwords on key accounts tied to that email |
| Clicked suspicious link | Disconnect device, run antivirus scan | Report message and review recent logins |
| Possible identity exposure | Contact bank, review credit report, consider freeze | Document incident and report to authorities |
Conclusion
Taking three clear actions today gives you lasting protection against common online threats. Start by securing your email, stop reusing the same login across online accounts, and enable multi-factor authentication where available.
Use a password manager or the built-in manager on your phone to create and store unique entries. Make a long passphrase (12–15+ characters) as your master, then update banking and health logins next.
Protecting your personal information also shields your family. Slow down when messages demand urgent action—type addresses yourself and check HaveIBeenPwned if you suspect a breach. Do a quick safety review monthly or quarterly.
These small steps add up to real control and calm. — Dan Alex
FAQ
Why are older adults often targeted online and why do your sign-in details matter today?
How do scammers use stolen logins to reach my money, health records, and Social Security information?
Why is email called the “master key” to my online life?
How do data breaches make reused sign-ins risky even if you didn’t do anything wrong?
What does a password actually protect, and how do criminals try to break it?
What’s the difference between “what you know,” “what you have,” and “who you are”?
What is single-factor versus multi-factor authentication in plain terms?
Can I make a strong passphrase quickly? What’s a simple method?
How long should my login be and what characters should I use?
What patterns should I avoid when creating a login?
Are there real examples of strong passphrases and why they work?
Why should you never reuse the same login across multiple accounts?
Which accounts are most dangerous to reuse a password on?
How can I keep unique passwords without writing them all down on sticky notes?
What is two-factor authentication (2FA) when a site texts you a code?
Why is an authentication app safer than text messages?
Which accounts should I enable multi-factor authentication on first?
How do I enable two-factor authentication on my phone?
What does a password manager do and why should you use one?
How do you pick a strong master password for your password manager?
Should I enable multi-factor authentication on my password manager too?
What recovery options should I set so I don’t get locked out of my password manager?
Is it ever okay to write down one password, and how do I store it safely at home?
When should you change a password and when is it unnecessary?
How can you spot a fake login page in email or text messages before entering credentials?
What are safer sign-in habits for banking and other sensitive accounts?
Why should you always log out on shared or public devices?
How can I check if my email or accounts were exposed in a data breach?
What immediate steps should you take if you think your password was stolen?
How do you regain control if your email was taken over?
What should you do if you clicked a suspicious link?
How can you protect your identity after a compromise?
Where can you report scams and phishing in the United States?
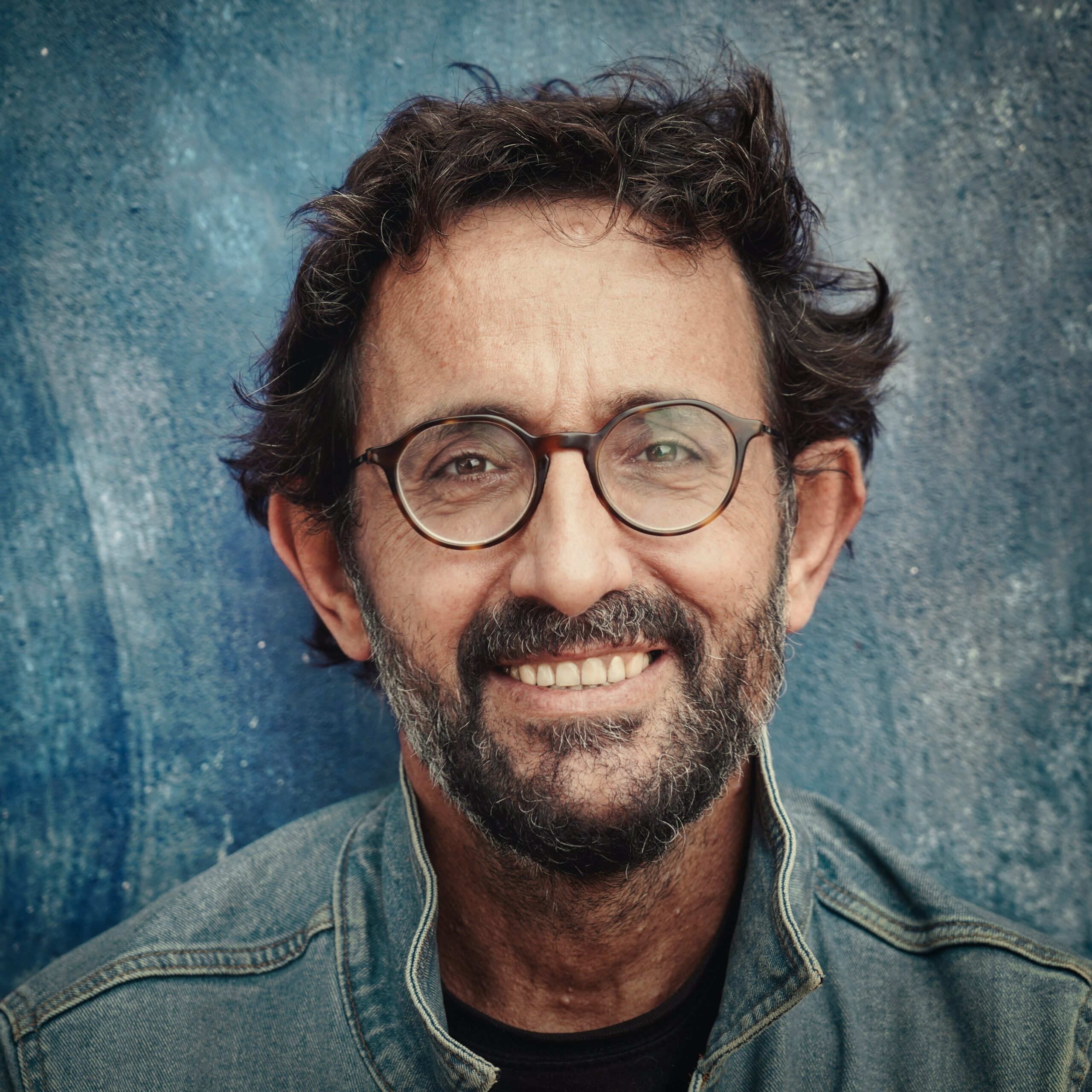
Dan Alex is a technology specialist and digital advocate with over 15 years of experience in system optimization and user experience (UX). Throughout his career, Dan has witnessed the frustration that rapid technological shifts cause for the senior community. As the founder of Apps for Download, Dan Alex combines his technical background with a passion for simplified education. His “human-first” approach to technology has made him a trusted voice for families and caregivers looking to empower their loved ones with digital tools.

